How to Image an Apple Silicon Mac with RECON ITR Live
Apple has made significant changes to the Mac lineup when transitioning from Intel processors to their Apple M1 Chip (Apple Silicon). Since then, forensic examiners have been confused about how to image and process Macs with Apple’s new proprietary processor.
At SUMURI, we want to put that confusion at ease by informing all forensic examiners that RECON ITR supports live imaging of Apple Silicon Macs. Since RECON ITR is developed on a Mac, it utilizes native macOS libraries to support new macOS file systems and artifacts quickly.
For more information about Apple Silicon Macs and Big Sur, click here: https://sumuri.com/big-sur-big-changes/
Macs with an Apple Silicon Processor
Mac computers with Apple Silicon:
- MacBook Pro (13-inch, M1, 2020)
- MacBook Air (M1, 2020)
- Mac Mini (M1, 2020)
To determine if a Mac has an Apple Silicon processor on a live system, navigate to the Apple Menu and click About This Mac to show the processor labeled next to Chip.*
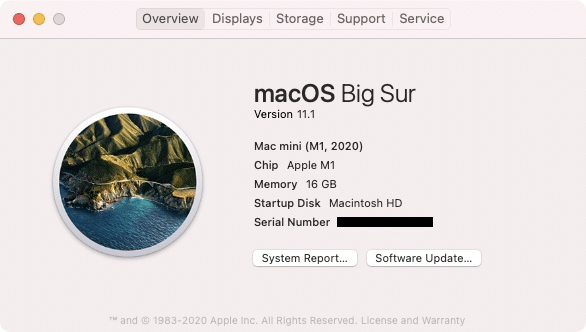
*On Intel-based Macs, it will be labeled as Processor. This Mac Imaging Guide (https://sumuri.com/mac-imaging-guide/) contains a decision tree on how to image Intel-based Macs.
Imaging an Apple Silicon Mac with RECON ITR Live
Apple Silicon Macs need to be imaged from the Desktop using RECON ITR’s Live Imager due to the new processors’ increased security. Examiners first need to obtain the administrator password of the Mac being imaged (without the password, examiners cannot image the Mac).
Ensure RECON ITR is updated to the most current version and grant the application Full Disk Access. For more information, please refer to Section 7 of the RECON ITR manual: https://sumuri.com/recon-itr-manual/.
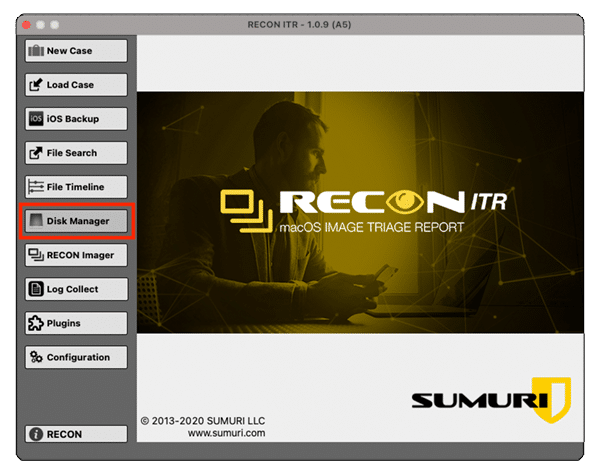
Run RECON ITR from the Samsung T7 SSD and open the Disk Manager.
Since Apple has made more changes to internal disks, determine the target internal synthesized disk before continuing to image. The Disk Manager view will vary depending on the configuration of the system.
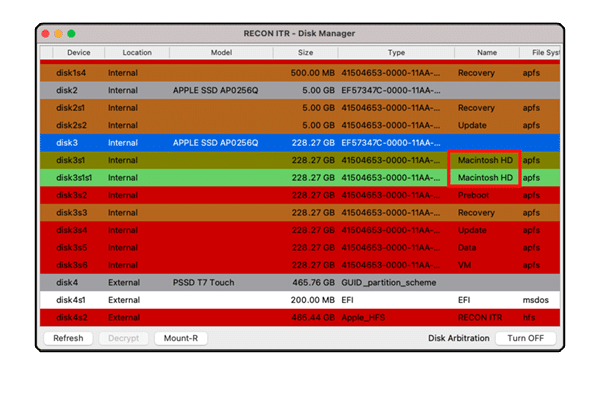
Ensure that the target synthesized disk includes the standard macOS partitions. The screenshot above displays disk3 as the internal synthesized disk that contains all of the standard partitions: Macintosh HD, Macintosh HD Data, Preboot, Recovery, etc.
After checking the target disk, close the Disk Manager window and launch RECON Imager to start Live imaging.
![]()
A window will appear to input the machine’s Admin password.
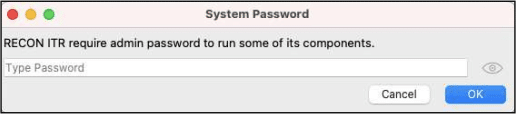
Once the Admin password is entered, RECON Imager will launch and display the Disk Imager menu.
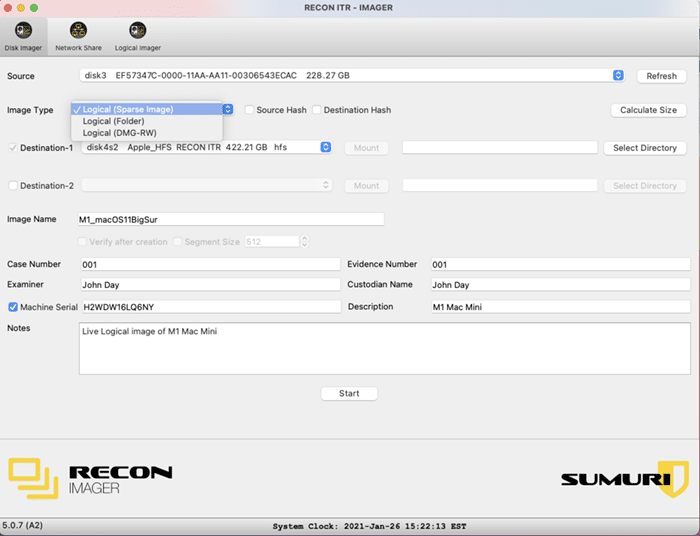
Select the Source and Image Type.
Image Types include:
- Logical (Sparse Image)* – A native macOS image format that is dynamically sized and can only be used within the Mac environment
- Logical (Folder) – A logical data extraction of the file system
- Logical (DMG-RW) – A native macOS image format that is static and can only be used within the Mac environment
* The recommended image format that works the best in RECON LAB.
Then, select the Destination Drive. We recommend using an HFS+ formatted Destination Drive for the best results.
Next, enter your case information in the section below.
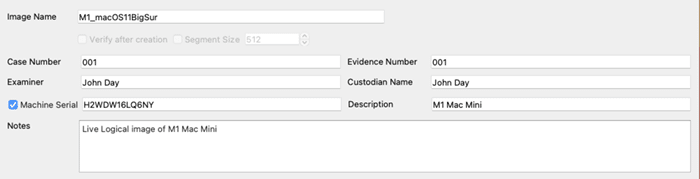
After filling out the case information, click Start to begin imaging.
![]()
Once the imaging finishes, take the image and process it in RECON LAB.
Images processed in RECON LAB keep the data in its native environment to properly parse Apple Extended Attribute metadata to see the correct timestamps.
RECON LAB utilizes native libraries that are proprietary to macOS for quicker support for new hardware.
RECON LAB is not like other traditional forensic tools ported from non-Mac operating systems that experience limitations such as missed data, improper interpretation of data, and slower processing times. Other tools rely on reverse engineering and third-party open-source and infrequently updated applications.
For more information on RECON LAB, click here: https://sumuri.com/software/recon-lab/.
Make sure to check out SUMURI’s other resources and blog posts to stay up to date with updates to the Mac Forensic environment.
Upcoming Courses
- By Chris Grettenberger
- Categories: Blog


Why Use a Mac for Mac Forensics