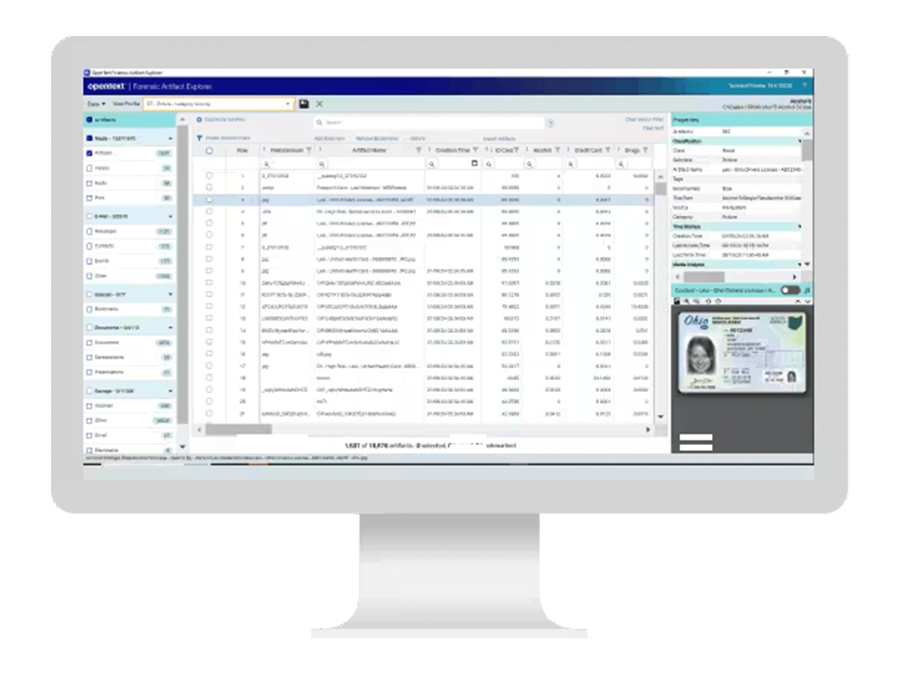
OpenText Forensic (EnCase)
Price:
OpenText EnCase Forensic is recognized globally as the standard for digital forensics and is a court-proven solution built for deep-level digital forensics investigation, powerful processing and integrated investigation workflows with flexible reporting options. It is built with a deep understanding of the digital investigation lifecycle and the importance of maintaining evidence integrity. EnCase Forensic empowers any examiner to seamlessly complete any investigation, including investigations of mobile devices.
OpenText EnCase Forensic – Product Overview & User Guide
Online Purchases and Pricing are for the US only. For International Purchases and Support Please Contact Us.
PRODUCT DESCRIPTION
OpenText EnCase Forensic provides reliable evidence acquisition by ensuring the integrity of collected data is preserved and stored in court-accepted evidence file formats. It delivers deep forensic analysis capabilities trusted in thousands of court cases, enabling investigators to uncover hidden evidence and analyze operating systems beyond standard artifact-based investigations. The platform also supports mobile collections for more than 36,000 smartphone and tablet profiles, allowing examiners to perform both logical and physical acquisitions with ease. Its advanced artificial intelligence image analysis technology helps categorize and identify potential contraband with near-zero false positives, while broad operating system, file system, artifact, and encryption support enables investigators to perform comprehensive and conclusive forensic investigations. In addition, EnCase Forensic allows digital investigators to connect to the cloud and collect evidence from cloud-based applications, social media platforms, storage services, and communication tools.
| Feature | Description |
|---|---|
| Enhanced indexing engine | Empowers investigators to conduct investigations with powerful processing speeds, advanced index searching, comprehensive language support and optimized performance. |
| Easy reporting | Provides customizable templates to help examiners create compelling, easy to read, professional reports that can be shared for every case. |
| Extensibility | Offers extensibility through EnScripts, which are automated code commands that streamline and automate tasks and extend the capabilities of EnCase Forensic to help examiners complete investigations more efficiently. |
| Workflow automation | Delivers automated investigation workflows so examiners can easily navigate through EnCase Forensic to enhance how they uncover evidence. |
| Updated encryption support | Provides encryption support for Microsoft® Windows® 10 BitLocker XTS-AES, Dell® Data Protection 8.17 and Symantec PGP 10.3; investigators can acquire encrypted evidence without worry about data corruption, damage or unnecessary delays. |
| Apple File System (APFS) support | Supports APFS, the file system used in helping investigators conduct targeted data collections from APFS and send the output as an EnCase logical evidence file. |
| Volume shadow copy capabilities | Examines Volume Shadow Snapshot (VSS) backups, also known as volume shadow copies, generated by Microsoft Windows, allowing investigators to recover deleted or modified files, as well as full volumes and learn what may have taken place on a system before the investigation. |
| Apple T2 Security Bypass | Acquires machines equipped with Apple T2 Security chips without additional hardware, drive partitions, or hassle. If the user is logged in, no credentials are required. |
| AFF4 support | Provides physical and logical read capabilities to allow for ingestion of evidence from other investigative tools, enabling all relevant evidence to be collected within a single EnCase case file and helping investigators quickly gain a more comprehensive view of the evidence available to their case. |
FREQUENTLY ASKED QUESTIONS (FAQ)
What is OpenText Forensic, and is it related to EnCase Forensic?
OpenText Forensic is a court-proven digital forensics investigation tool used primarily by law enforcement, government agencies, and forensic labs. It allows investigators to acquire, preserve, analyze, and report on data from computers, mobile devices, and storage media while maintaining forensic integrity. OpenText Forensic is part of an entire family of OpenText DFIR solutions.
OpenText Forensic is the same product as EnCase Forensic. EnCase Forensic was renamed to align with the OpenText cybersecurity portfolio and as part of a corporate-wide rebranding initiative.
How does OpenText Forensic ensure data integrity during an investigation?
The solution uses industry-standard forensic image formats (E01, L01) and applies hashing algorithms to ensure the authenticity of data. All actions are logged to maintain a strict chain of custody, supporting court-admissible evidence collection.
How does OpenText Forensic handle encrypted data?
OpenText Forensic supports decryption workflows for common encryption types and integrates with password recovery tools. It can detect encryption at the volume, file, or container level and supports forensic acquisition of encrypted devices.
What are the licensing models or deployment options for OpenText Forensic?
OpenText Forensic supports a one-year term-based licensing model. It is an on-premises solution that is either deployed via a USB license, on the network, or via an electronic license key.
What types of devices and media can OpenText Forensic analyze?
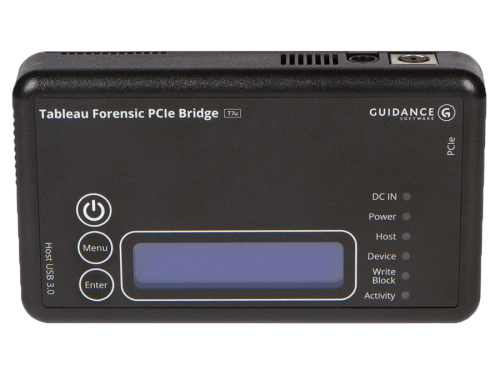
OpenText Forensic supports a wide range of devices and file systems, including Windows®, macOS®, Linux®, removable drives, encrypted volumes, cloud storage, and mobile device backup files. Its broad compatibility makes it a go-to solution for diverse forensic environments.
Can OpenText Forensic recover deleted or hidden files?
Yes. OpenText Forensic includes advanced data carving, unallocated space analysis, and artifact parsing to recover deleted files, hidden partitions, and remnants of user activity that standard tools may miss.
Does OpenText Forensic support mobile device investigations?
Yes. It supports mobile forensic workflows by analyzing iOS and Android backup files, including app data, messages, and call history. For deeper mobile analysis, it is often used in conjunction with OpenText™ Mobile Investigator .
What makes OpenText Forensic different from OpenText™ Endpoint Investigator?
OpenText Forensic is designed for lab-based forensic analysis of seized or powered-off devices. It excels in deep, offline investigations with a broad range of supported formats. In contrast, OpenText™ Endpoint Investigator and OpenText™ Endpoint Forensics and Response are DFIR solutions tailored for enterprise environments, enabling remote, live endpoint investigations and real-time incident response.